- I recommend the Pixel 9 to most people looking to upgrade - especially while it's $250 off
- Google's viral research assistant just got its own app - here's how it can help you
- Sony will give you a free 55-inch 4K TV right now - but this is the last day to qualify
- I've used virtually every Linux distro, but this one has a fresh perspective
- The 7 gadgets I never travel without (and why they make such a big difference)
Threat Actors Are Exploiting Vulnerabilities Faster Than Ever

New research by cybersecurity firm Mandiant provides eyebrow-raising statistics on the exploitation of vulnerabilities by attackers, based on an analysis of 138 different exploited vulnerabilities that were disclosed in 2023.
The findings, published on Google Cloud’s blog, reveals that vendors are increasingly being targeted by attackers, who are continually reducing the average time to exploit both zero-day and N-day vulnerabilities. However, not all vulnerabilities are of equal value to attackers, as their significance depends on the attacker’s specific objectives.
Time-to-exploit is falling significantly
Time-to-exploit is a metric that defines the average time taken to exploit a vulnerability before or after a patch is released. Mandiant’s research indicates:
- From 2018 to 2019, the TTE sat at 63 days.
- From 2020 to 2021, it fell to 44 days.
- From 2021 to 2022, the TTE dropped even further to 32 days.
- In 2023, the TTE sat at just 5 days.
SEE: How to Create an Effective Cybersecurity Awareness Program (TechRepublic Premium)
Zero-day vs N-day
As TTE continues to shrink, attackers are increasingly taking advantage of both zero-day and N-day vulnerabilities.
A zero-day vulnerability is an exploit that hasn’t been patched, often unknown to the vendor or the public. An N-day vulnerability is a known flaw first exploited after patches are available. It is therefore possible for an attacker to exploit a N-day vulnerability as long as it has not been patched on the targeted system.
Mandiant exposes a ratio of 30:70 of N-day to zero-days in 2023, while the ratio was 38:62 across 2021-2022. Mandiant researchers Casey Charrier and Robert Weiner report that this change is likely due to the increased zero-day exploit usage and detection rather than a drop in N-day exploit usage. It is also possible that threat actors had more successful attempts to exploit zero-days in 2023.
“While we have previously seen and continue to expect a growing use of zero-days over time, 2023 saw an even larger discrepancy grow between zero-day and n-day exploitation as zero-day exploitation outpaced n-day exploitation more heavily than we have previously observed,” the researchers wrote.
N-day vulnerabilities are mostly exploited in the first month after the patch
Mandiant reports that they observed 23 N-day vulnerabilities being exploited in the first month following the release of their fixes, yet 5% of them were exploited within one day, 29% within one week, and more than half (56%) within a month. In total, 39 N-day vulnerabilities were exploited during the first six months of the release of their fixes.

More vendors targeted
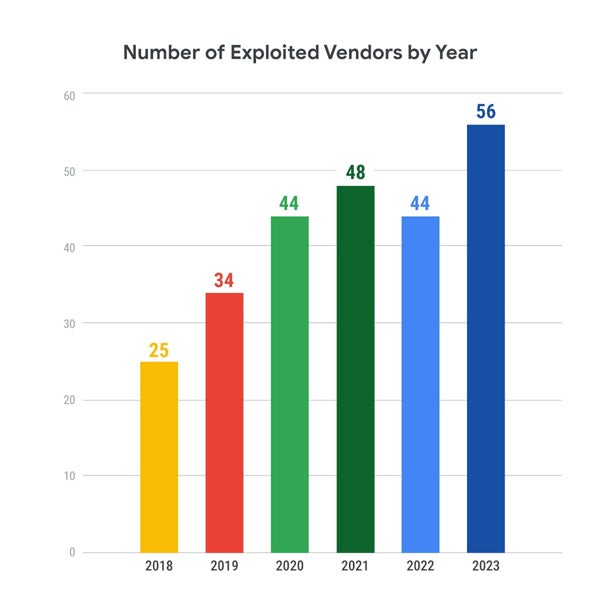
Attackers seem to add more vendors to their target list, which increased from 25 vendors in 2018 to 56 in 2023. This makes it more challenging for defenders, who try to protect a bigger attack surface every year.
Cases studies outline the severity of exploitations
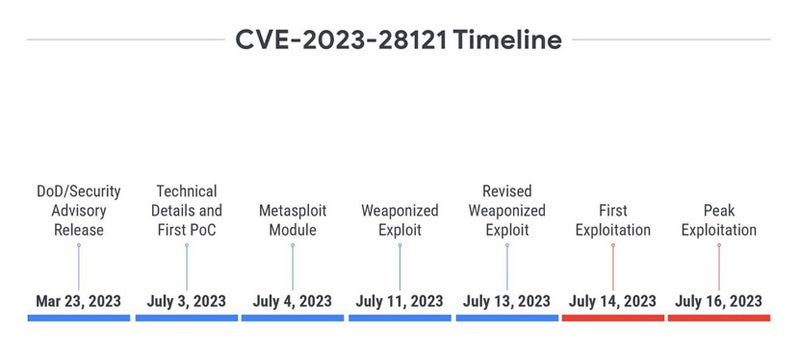
Mandiant exposes the case of the CVE-2023-28121 vulnerability in the WooCommerce Payments plugin for WordPress.
Disclosed on March 23, 2023, it did not receive any proof of concept or technical details until more than three months later, when a publication showed how to exploit it to create an administrator user without prior authentication. A day later, a Metasploit module was released.
A few days later, another weaponized exploit was released. The first exploitation began one day after the revised weaponized exploit had been released, with a peak of exploitation two days later, reaching 1.3 million attacks on a single day. This case highlights “an increased motivation for a threat actor to exploit this vulnerability due to a functional, large-scale, and reliable exploit being made publicly available,” as stated by Charrier and Weiner.
The case of CVE-2023-27997 is different. The vulnerability, known as XORtigate, impacts the Secure Sockets Layer (SSL) / Virtual Private Network (VPN) component of Fortinet FortiOS. The vulnerability was disclosed on June 11, 2023, immediately buzzing in the media even before Fortinet released their official security advisory, one day later.
On the second day after the disclosure, two blog posts were published containing PoCs, and one non-weaponized exploit was published on GitHub before being deleted. While interest seemed apparent, the first exploitation arrived only four months after the disclosure.
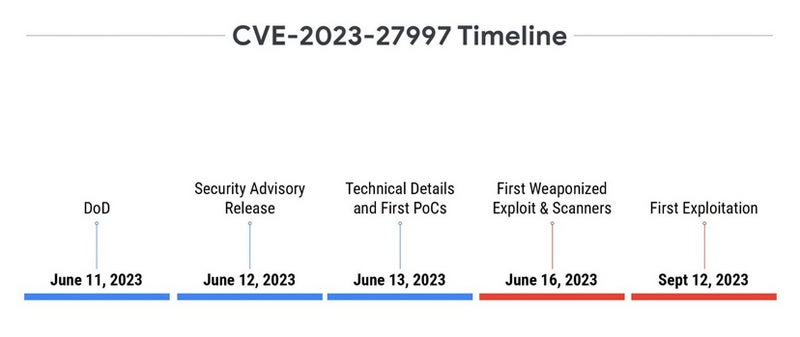
One of the most likely explanations for the variation in observed timelines is the difference in reliability and ease of exploitation between the two vulnerabilities. The one affecting WooCommerce Payments plugin for WordPress is easy to exploit, as it simply needs a specific HTTP header. The second is a heap-based buffer overflow vulnerability, which is much harder to exploit. This is especially true on systems that have several standard and non-standard protections, making it difficult to trigger a reliable exploitation.
A driving consideration, as exposed by Mandiant, also resides in the intended utilization of the exploit.
“Directing more energy toward exploit development of the more difficult, yet ‘more valuable’ vulnerability would be logical if it better aligns with their objectives, whereas the easier-to-exploit and ‘less valuable’ vulnerability may present more value to more opportunistic adversaries,” the researchers wrote.
Deploying patches is no simple task
More than ever, it is mandatory to deploy patches as soon as possible to fix vulnerabilities, depending on the risk associated with the vulnerability.
Fred Raynal, chief executive officer of Quarkslab, a French offensive and defensive security company, told TechRepublic that “Patching 2-3 systems is one thing. Patching 10,000 systems is not the same. It takes organization, people, time management. So even if the patch is available, a few days are usually needed to push a patch.”
Raynal added that some systems take longer to patch. He took the example of mobile phone vulnerability patching: “When there is a fix in Android source code, then Google has to apply it. Then SoC makers (Qualcomm, Mediatek etc.) have to try it and apply it to their own version. Then Phone makers (eg Samsung, Xiaomi) have to port it to their own version. Then carriers sometimes customize the firmware before building it, which can not always use the latest versions of the source. So, here, the propagation of a patch is … long. It is not uncommon to find 6 month old vulnerabilities in today’s phone.”
Raynal also insists that availability is a key factor in deploying patches: “Some systems can afford to fail! Consider an oil platform or any energy maker: patching ok, but what if the patch creates a failure. No more energy. So what is the worst? An unpatch critical system or a city without energy? An unpatch critical system, it is about a potential threat. A city without energy, it is about actual issues.”
Finally, some systems are not patched at all, according to Raynal: “In some areas, patches are forbidden. For instance, many companies building healthcare devices prevent their users from applying patches. If they do, it breaks the warranty.”

